1. what is pptp?
pptp (point-to-point tunneling protocol) is a widely used vpn protocol mainly used to establish secure connections in insecure networks. it ensures the security of data transmission by establishing an encrypted channel between the user's computer and the vpn server. although pptp performs well in terms of speed and ease of use, its security has always been controversial.
2. how secure is pptp on us servers?
using the pptp protocol on a us server is less secure than other protocols such as openvpn or l2tp/ipsec. although the mppe (microsoft point-to-point encryption) technology used by pptp can provide basic encryption, its encryption strength is relatively weak and vulnerable to brute force cracking and other attacks. in addition, the authentication mechanism of the pptp protocol also has some loopholes, making it insecure in the face of advanced attacks.
3. what are the advantages and disadvantages of using pptp us server?
the advantages of using a pptp us server include: first, the setup is simple and the connection speed is fast, which is suitable for users with high speed requirements. secondly, since pptp is widely supported on various devices, users can easily use it on different platforms. however, the disadvantage is that it has low security and is not suitable for occasions that require high security protection. in addition, pptp has strong firewall penetration capabilities, but this may also lead to increased security risks.
4. how to improve the security of pptp connection?
while the security of pptp itself is limited, there are steps users can take to improve its security. first, make sure you use strong passwords for authentication and avoid simple, easy-to-guess passwords. second, it can be combined with other security measures, such as the use of firewalls and anti-virus software, to improve overall security. in addition, it is also very important to regularly update vpn client and server software to patch known security vulnerabilities.
5. under what circumstances is pptp not recommended?
if the user's main need is to protect sensitive information, then it is recommended to avoid using pptp us servers . for example, when conducting online banking, processing personal privacy data, or communicating business secrets, the security of pptp is not sufficient to ensure data security. at this point, users should choose more secure vpn protocols, such as openvpn or wireguard, which provide stronger encryption and security.
- Latest articles
- Japanese Cloud Server Vendor Security Compliance Certification And Encrypted Transmission Practice Guide
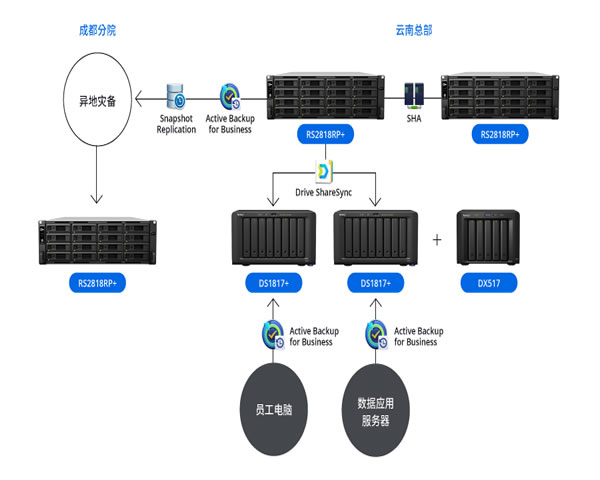
- Detailed Explanation Of Enterprise Migration To Alibaba Cloud Malaysia Server Disaster Recovery Plan And Data Synchronization
- Comparison Of Model Selection And Analysis Of The Differences In Encoding, Transcoding And Delay Of Us High-bandwidth Server Video From Different Manufacturers
- A Case Study On The Combination Of Caching And Cdn Explains How Malaysia Optimizes Servers To Improve Concurrent Processing Capabilities
- Service Agreements And Commitments You Need To Pay Attention To When Choosing The Us High-defense Server 100g
- Is South Korea's Cn2 Us Dedicated Line A Test Of Its Actual Impact On Game And Live Broadcast Delays?
- How To Judge Which Vps Korea Or Japan Node Is More Suitable For You Based On Usage
- Business Case Shows How Hong Kong Server High-defense Improves Business Stability After Selection
- Which Business Scenarios Are Suitable For Korean Vps Native Ip And Bandwidth Selection Suggestions?
- Vpn Configuration And Tunnel Stability Alternative Solutions When The Cf Vietnam Server Cannot Be Accessed
- Popular tags
-
Compliance Advice: Exclusive Records And Evidence Retention Requirements For Us Ip Servers In Compliance Audits
a practical guide on record and evidence preservation for exclusive us ip servers in compliance audits, including detailed steps for configuration, log collection, tamper-proof preservation, backup strategy, link evidence, packaging delivery and legal precautions. -
How To Protect Trade Secret Data In Us High-defense Server Security Transactions
this article, written by a professional cybersecurity consultant, details practical strategies for protecting commercial confidential data when using u.s. high-defense servers for secure transactions, including encryption, access control, compliance, and vendor auditing. -
Optimization Method: Us Free Server Download Security Patch And Performance Update Process
this article systematically explains the us free server download channels, server security patch management and performance update process, covering vps, host, domain name, cdn and high-defense ddos protection suggestions, and provides purchase and deployment suggestions, recommending dexun telecom services.